Why Operator-Led Training?
Our instructors aren't career trainers — they're operators who've conducted real cyber operations at the highest levels.
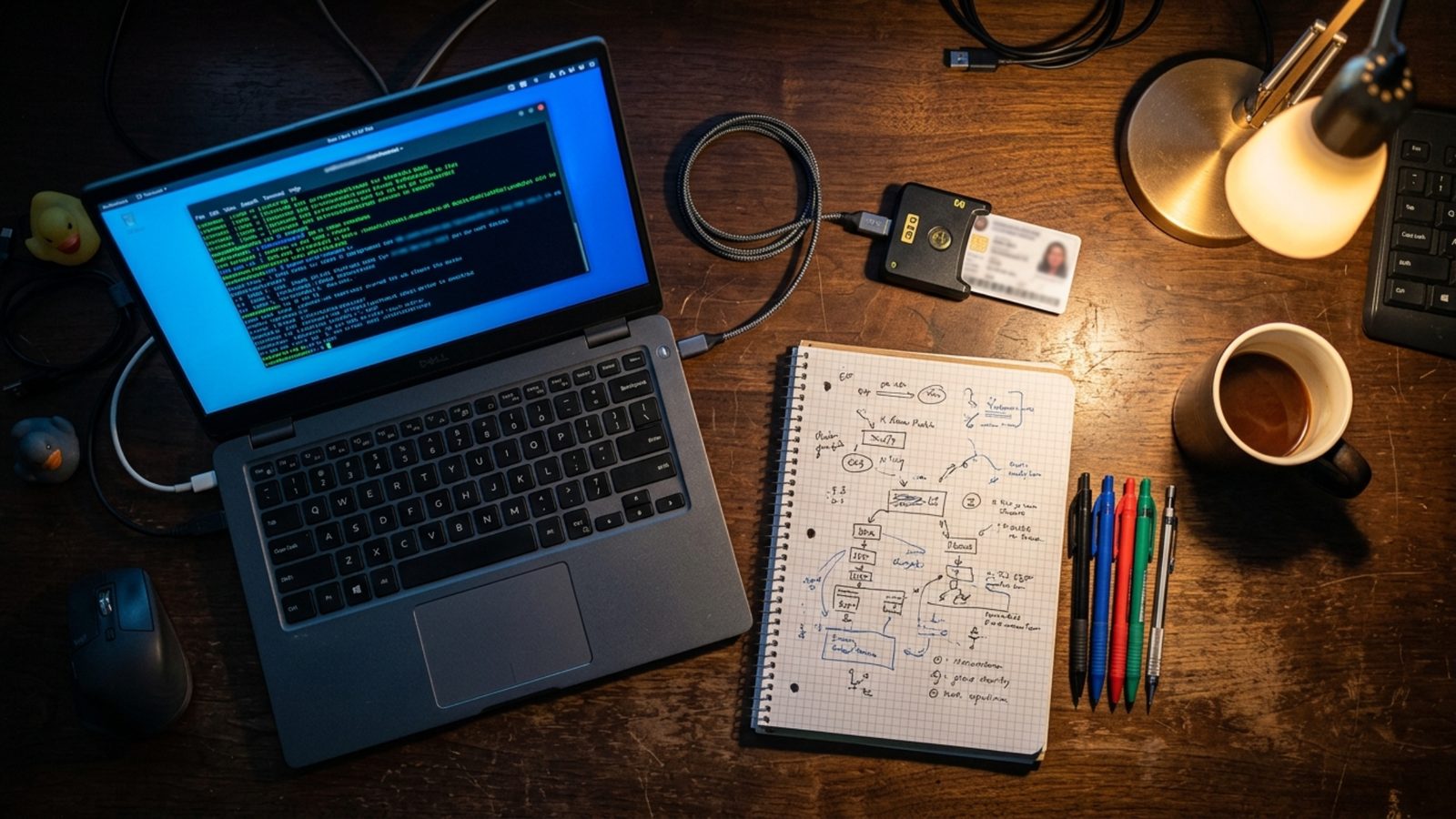
Real-World Experience
Every course is based on actual tactics, techniques, and procedures used in real operations. We don't teach from textbooks — we teach from experience.
Hands-On Labs
Our training includes hands-on lab environments, cyber ranges, and simulations that mirror real-world scenarios. You'll practice defending against actual attack techniques.